Nobody likes an eavesdropper. Businesses and homeowners alike deserve their privacy. However, your home, business, car, or even your boat may be collecting unauthorized audio and video footage right now from beneath your nose. For this reason, security and IT firms have begun making TSCM equipment available through their services to assure individuals that their conversations and property remain private.
What is TSCM?
Before we get into the TSCM equipment that will be used to debug your property, let’s focus on what TSCM actually is.
Technical Surveillance Countermeasures
TSCM stands for technical surveillance countermeasures. These are highly-specialized actions (or sweeps) that detect the presence of eavesdropping devices such as hidden cameras or covert microphones. The techniques involved with using TSCM can help you effectively detect and nullify the technology that has stolen unauthorized access to your info.
Illicit Intelligence
As the corporate market gets more and more competitive, bugging and eavesdropping measures have become more hostile than ever. Knowledge is power, and unethical organizations and individuals are willing to do whatever it takes to obtain that knowledge; your knowledge. If you’re running a business, you don’t want your competitors using your customer’s contact information, do you? Enlist the aid of a professional TSCM team to stay ahead of the curve and keep your data safe.
TSCM Equipment
Skilled investigative teams will use a variety of sweeping equipment to protect your privacy and exploit any vulnerabilities in your security. With technology constantly evolving, professional TSCM teams keep their equipment up-to-date to address any emerging threats or new technological trends.
High-Quality and Modern Design
From GPS tools and network analysis to threat-level programming and spectrum software, TSCM investigators utilize cutting-edge technology to provide clients with the highest level of service. They put the technical into technical surveillance countermeasures.
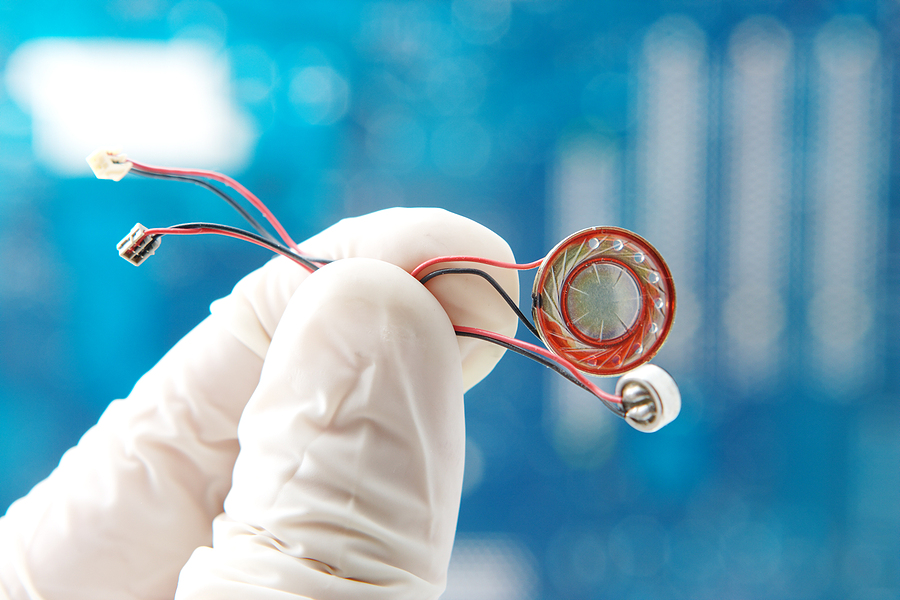
Especially considering that most modern surveillance technologies are incredibly discreet, capable, and difficult to locate, TSCM equipment needs to be optimized for a successful sweep. Bugs are typically scanned by hand-held tools with specialized software. Physical security, wireless intrusion detection systems, and in-place monitoring systems are also used to protect your privacy.
What Is TSCM Equipment Used For?
As previously discussed, TCSM equipment is used to perform a range of surveillance sweeps. Depending on what you need it for, TSCM can be used to provide:
- Communications security
- Technical security
- Eavesdropping detection
- Anti-surveillance services
- Wiretap detection
- Camera detection
What Happens Next?
Ultimately, all of your property, data, equipment, phone lines, instruments, devices, and networks will be processed thoroughly and completely. A successful sweep will detect any unwanted bugs in order to keep your business or personal information safe and secure.
Additionally, if any intrusions on your internal communication are discovered, investigative professionals will determine if it constitutes a security breach If that is the case, they will help you build a case against the perpetrators.

Are You Ready to Put TSCM Equipment to Use?
If you suspect your home, business, car, or even your boat is being watched or listened to without your consent, call South and Associates for a free consultation.
The Investigative Services You Need
The experienced investigators on our team have the knowledge to effectively protect your assets and privacy. Whether you need debugging and eavesdropping detection conducted or require help with more personal matters such as infidelity and alimony, South and Associates will provide the investigative and security solutions you need in a timely manner.
It’s time to sweep, squash bugs, and keep your personal data secure. Reach out today to keep your conversations and information private: the way it should be.
